Bash, Applescript, and Sshuttle (Python): Creating a multi-jump into the multiverse...
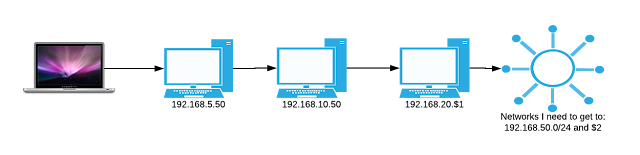
via GIPHY Summary: Basically, I work through VPN's most of my existence. The problem lies when I have to switch to different VPN's it disrupts my communications w/ other tools that only exist in one VPN, but not the other. There does appear to be tools around some of these things, but I wanted something quick and dirty. AND DIRTY it is. This enables me to stay connected to the main VPN and cheat by sshuttle'ing through systems of access temporarily. Details: I'm using MACOS and to launch a terminal in a new window turned me on to AppleScript. I wanted to pass two variables. 1st was basically an identifier for the end system I wanted to shuttle my traffic through. 2nd was to pass a password variable to any system inbetween that was not setup w/ my SSH public key. So I made a bash function, to call applescript to open my terminals to run what is effectively a python binary. It works, but has several prerequisites for it to run smoothly....
