Bash, Applescript, and Sshuttle (Python): Creating a multi-jump into the multiverse...
Summary:
Basically, I work through VPN's most of my existence. The problem lies when I have to switch to different VPN's it disrupts my communications w/ other tools that only exist in one VPN, but not the other. There does appear to be tools around some of these things, but I wanted something quick and dirty. AND DIRTY it is. This enables me to stay connected to the main VPN and cheat by sshuttle'ing through systems of access temporarily.
Details:
I'm using MACOS and to launch a terminal in a new window turned me on to AppleScript. I wanted to pass two variables.
1st was basically an identifier for the end system I wanted to shuttle my traffic through.
2nd was to pass a password variable to any system inbetween that was not setup w/ my SSH public key.
So I made a bash function, to call applescript to open my terminals to run what is effectively a python binary. It works, but has several prerequisites for it to run smoothly. The nice thing about this script, it demonstrates the utility of a bash function and how you can make use of AppleScript.
Would any sane person need this? Probably not, but who am I to judge.
PreReqs:
- sshuttle
- visudo modifications (optional), but useful.
- Cmnd_Alias for sshuttle so you can define a NOPASSWD sudo'er for sshuttle ONLY
- This is super important, because you don't want to enable NOPASSWD for all applications. Although I don't know why I stress this point since I'm probably breaking so many security rules as it is. Oh well.
-
Cmnd_Alias SSHUTTLE = /usr/bin/env PYTHONPATH=/usr/local/Cellar/sshuttle/0.78.5/libexec/lib/python3.7/site-packages /usr/local/Cellar/sshuttle/0.78.5/libexec/bin/python3.7 /usr/local/bin/sshuttle --method auto --firewall
-
yourUsername ALL=(root) NOPASSWD: SSHUTTLE
- SSHHostKeyChecking (Optional) disable
- I'm going to change this later, but as a quick and dirty, I'm basically saying I don't care about security because I KNOW the endpoints I'm connecting to. Need to make it a bit more strict, but the goal is to skip the "yes" I accept the host key automatically.
- ~/.ssh/config
-
Host *StrictHostKeyChecking noUserKnownHostsFile=/dev/null
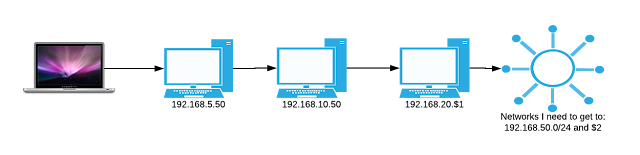
Effectively there is either no route or firewall preventing access to the networks I need to get to. This diagram basically demonstrates how I can use shuttle to proxy my mac to the networks I need.
Script:



Comments
Great script - working on something similar